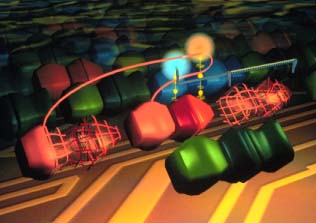
 A hyper-parasite (red, three piece object) steals the CPU from
a parasite (blue sphere). Using the stolen CPU, and its own CPU (red
sphere) it is able to produce two daughters (wire frame objects on left
and right) simultaneously.
A hyper-parasite (red, three piece object) steals the CPU from
a parasite (blue sphere). Using the stolen CPU, and its own CPU (red
sphere) it is able to produce two daughters (wire frame objects on left
and right) simultaneously.
Because informational parasitism involves the execution of code belonging to another digital organism, it creates a vulnerability that has been exploited by a new class of adaptations. Certain ``hosts'' have evolved a means of capturing the CPUs of parasites that execute their code, in effect, parallelizing themselves by stealing CPUs from parasites. The presence of these ``hyper-parasites'' in the environment can lead to the rapid elimination of parasites.
Figure 10:
 A hyper-parasite (red, three piece object) steals the CPU from
a parasite (blue sphere). Using the stolen CPU, and its own CPU (red
sphere) it is able to produce two daughters (wire frame objects on left
and right) simultaneously.
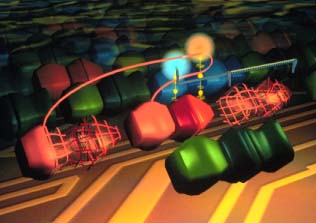
A hyper-parasite (red, three piece object) steals the CPU from
a parasite (blue sphere). Using the stolen CPU, and its own CPU (red
sphere) it is able to produce two daughters (wire frame objects on left
and right) simultaneously.